Bios Agent Plus Full Espaã±ol Crack Serial
Configure Posture
The AnyConnect Secure Mobility Client offers an VPN Posture (HostScan) Module and an ISE Posture Module. Both provide the Cisco AnyConnect Secure Mobility Client with the ability to assess an endpoint's compliance for things like antivirus, antispyware, and firewall software installed on the host. You can then restrict network access until the endpoint is in compliance or can elevate local user privileges so they can establish remediation practices.
VPN Posture is bundled with hostscan_version.pkg, which is the application that gathers what operating system, antivirus, antispyware, and software is installed on the host. ISE Posture deploys one client when accessing ISE-controlled networks, rather than deploying both AnyConnect and the NAC Agent. ISE Posture is a module you can choose to install as an additional security component into the AnyConnect product. HostScan, which was part of the AnyConnect bundle in release 3.x, is now a separate install.
ISE Posture performs a client-side evaluation. The client receives the posture requirement policy from the headend, performs the posture data collection, compares the results against the policy, and sends the assessment results back to the headend. Even though ISE actually determines whether or not the endpoint is compliant, it relies on the endpoint's own evaluation of the policy.
In contrast, HostScan performs server-side evaluation where the ASA asks only for a list of endpoint attributes (such as operating system, IP address, registry entries, local certificates, and filenames), and they are returned by HostScan. Based on the result of the policy's evaluation, you can control which hosts are allowed to create a remote access connection to the security appliance.
 Note | The combined use of HostScan and ISE posture agent is not supported. Unexpected results occur when two different posture agents are running. |
The following posture checks are supported in HostScan but not ISE Posture: Hostname, IP address, MAC address, port numbers, OPSWAT version, BIOS serial number, file check with checksum validation, personal firewall, and certificate field attributes.
What ISE Posture Module Provides
Posture Checks
The ISE Posture module uses the OPSWAT v3 library to perform posture checks. With an initial posture check, any endpoint that fails to satisfy all mandatory requirements is deemed non-compliant. The other endpoint authorization states are posture unknown or compliant (meeting mandatory requirements).
If an error occurs during the posture checking phase and AnyConnect is able to continue, the user is notified, but posture checking continues, if possible. If the error occurs during a mandatory posture check, the check is marked as failed. Network access is granted if all mandatory requirements are satisfied. If not, the user can restart the posture process.
Any Necessary Remediation
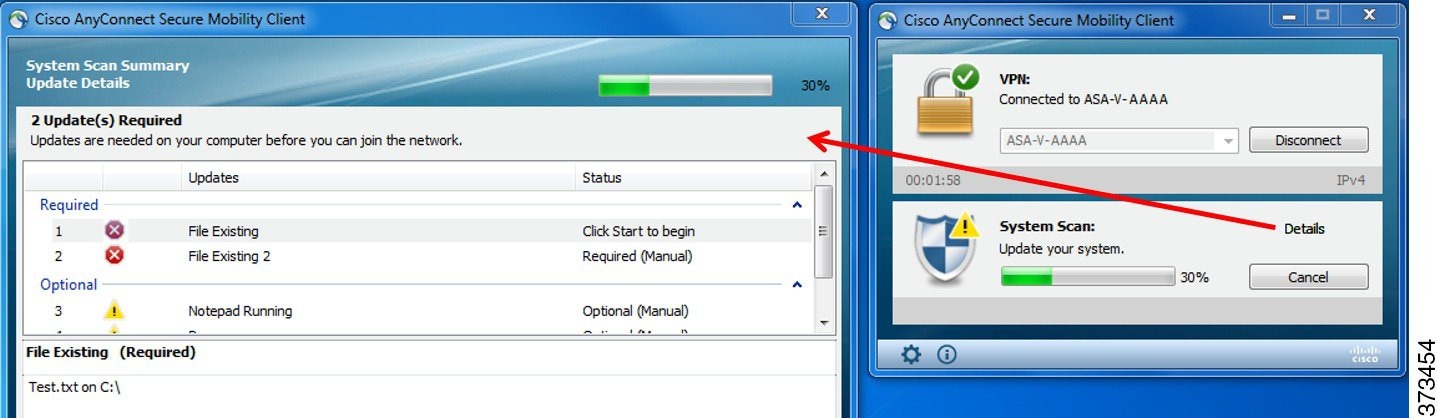
The remediation window runs in the background so that the updates on network activity do not pop up and interfere or cause disruption. You can click Details in the ISE Posture tile portion of the AnyConnect UI to see what has been detected and what updates are needed before you can join the network. If a required manual remediation is necessary, the remediation window opens, displaying the items that require action. This System Scan Summary window shows the progress of the updates, the time left of the allotted update time, the status of any requirements, and the system compliance state.
An administrator can configure a Network Usage Policy that displays at the end of the ISE Posture process. When accessing the policy, you see any required terms and conditions that the user must accept before access is granted to the access VLAN.
When only optional updates are left, you can choose to Skip to the next one or Skip All to disregard all remaining remediations. You can skip the optional remediations in the interest of time and still maintain network access.
After remediation (or after requirement checks when no remediation was needed), you may get an Acceptable Use Policy notification. It requires you to accept the policy for network access and limits access if you reject it. During this part of remediation, the Posture tile portion of the AnyConnect UI displays "System Scan: Network Acceptable Use Policy."
When remediation is complete, all of the checks listed as required updates appear with a Done status and a green checkbox. After remediation, the agent sends the posture result to ISE.
 Note | Because of architectural changes in Symantec products, ISE posture cannot support remediation from Symantec AV 12.1.x and onwards. |
Patch Management Checks and Remediation
The AnyConnect 4.x and Microsoft System Center Configuration Manager (SCCM) integration provides patch management checks and patch management remediation. It checks the state of critical patches missing on the endpoint to see if a software patch should be triggered. If no critical patches are missing on the Windows endpoint, the patch management check passes. Patch management remediation triggers only for administrator-level users and only if one or more critical patches are missing on the Windows endpoint.
Refer to Policy Conditions to learn how to set up policy conditions on ISE or Patch Management Remediation for further information on patch management remediation.
Reassessment of Endpoint Compliance
After the endpoint is deemed compliant and is granted network access, the endpoint can optionally be periodically reassessed based on what controls the administrator configured. The passive reassessment posture checks differ from the initial posture checks. If any fail, the user is given the option to remediate, if the administrator had the setting configured as such. The configuration settings control whether or not the user maintains trusted network access, even when one or more mandatory requirements have not been met. With initial posture assessment, failing to satisfy all mandatory requirements deems the endpoint non-compliant. This feature is set to disabled by default, and if enabled for a user role, it reassesses the posture every 1 to 24 hours.
The administrator can set the outcome to Continue, Logoff, or Remediate and can configure other options such as enforcement and grace time.
Automatic Compliance
With posture lease, the ISE server can skip posture completely and simply put the system into compliant state. With this functionality, users do not experience delays switching between networks when their system has recently been postured. The ISE Posture agent simply sends a status message to the UI shortly after the ISE server is discovered, indicating whether the system is compliant. In the ISE UI (in Settings > Posture > General Settings), you can specify an amount of time when an endpoint is considered posture compliant after an initial compliance check. The compliance status is expected to be preserved even when users switch from one communicating interface to another.
 Note | With a posture lease, if the session is valid on ISE, the endpoint is expected to go from posture unknown state to compliant state. |
VLAN Monitoring and Transitioning
Some sites use different VLANs or subnets to partition their network for corporate groups and levels of access. A change of authorization (CoA) from ISE specifies a VLAN change. Changes can also happen due to administrator actions, such as session termination. To support VLAN changes during wired connections, configure the following settings in the ISE Posture profile:
-
VLAN Detection Interval— Determines the frequency with which the agent detects a VLAN transition and whether monitoring is disabled. VLAN monitoring is enabled when this interval is set to something besides 0. Set this value to at least 5 for macOS.
VLAN monitoring is implemented on both Windows and macOS, although it is only necessary on macOS for the detection of unexpected VLAN changes. If a VPN is connected or an acise (the main AnyConnect ISE process) is not running, it disables automatically. The valid range is 0 to 900 seconds.
-
Enable Agent IP Refresh—When unchecked, ISE sends the Network Transition Delay value to the agent. When checked, ISE sends DHCP release and renew values to the agent, and the agent does an IP refresh to retrieve the latest IP address.
- DHCP Release Delay and DHCP Renew Delay— Used in correlation with an IP refresh and the Enable Agent IP Refresh setting. When you check the Enable Agent IP Refresh checkbox and this value is not 0, the agent waits for the release delay number of seconds, refreshes the IP addresses, and waits for the renew delay number of seconds. If a VPN is connected, IP refresh is automatically disabled. If 4 consecutive probes are dropped, it triggers a DHCP refresh.
-
Network Transition Delay— Used when VLAN monitoring is disabled or enabled by the agent (in the Enable Agent IP Refresh checkbox). This delay adds a buffer when a VLAN is not used, giving the agent an appropriate amount of time to wait for an accurate status from the server. ISE sends this value to the agent. If you also have the Network Transition Delay value set in the global settings on the ISE UI, the value in the ISE Posture Profile Editor overwrites it.
 Note | The ASA does not support VLAN changes, so these settings do not apply when the client is connected to ISE through an ASA. |
Troubleshooting
If the endpoint device cannot access the network after posture is complete, check the following:
-
Is the VLAN change configured on the ISE UI?
-
If yes, is DHCP release delay and renew delay set in the profile?
-
If both settings are 0, is Network Transition Delay set in the profile?
-
Operations That Interrupt the AnyConnect ISE Flow
For various reasons, the AnyConnect ISE Posture flow can be interrupted during either initial posture reassessment or passive reassessment.
- User Cancels AnyConnect ISE—During the period of posture checking and remediation, the user can cancel AnyConnect ISE. The UI immediately notifies a user that a cancellation is in progress, but it should occur only during a time that avoids putting the endpoint into a questionable state. Some cancellations may require a reboot if third-party software was used. The Posture tile portion of the AnyConnect UI shows the compliance state after the cancellation.
- Remediation Timer Expires—The administrator-controlled time to satisfy posture requirements has expired. An assessment report is sent to the headend. During passive reassessment, the user retains network access, and with posture assessment, network access is granted when all mandatory requirements are satisfied.
- Error During Posture Checking—If an error occurs during the posture checking phase and AnyConnect is able to continue, the user is notified, but posture checking continues, if possible. If the error occurs during a mandatory posture check, the check is marked as failed. Network access is granted if all mandatory requirements are satisfied. If not, the user can restart the posture process.
- Error During Remediation—If an error occurs during the remediation phase and AnyConnect ISE Posture can continue, the user is notified. AnyConnect ISE Posture stops the remediation process if the failed remediation step is associated with a mandatory posture requirement. If the failed remediation step is associated with an optional posture requirement, it attempts to continue with the next step and finish the ISE Posture operation. Network access is granted if all mandatory requirements are satisfied. If not, the user can restart the posture process.
- Default Gateway Change—A user might lose trusted network access because of a change to the default gateway, causing the ISE Posture to attempt a rediscovery of ISE. The ISE Posture tile portion on the AnyConnect UI displays the status of ISE Posture when it goes into rediscovery mode.
- Loss of Connectivity Between AnyConnect and ISE—After the endpoint is deemed compliant and granted network access, various network scenarios can occur: the endpoint can experience complete loss of network connectivity, ISE could go down, the ISE posture could fail (because of a session timeout, manual restart, or the like), or ISE behind an ASA may lose the VPN tunnel.
-
You cannot have multiple console users logged in on a macOS endpoint when using ISE posture.
-
Delays in Initalization and Posture Assessment Flow (macOS only)—Apple advises you to allow their subnet in the pre-posture phase so that failures with signature verification of Compliance Module libraries won't occur.
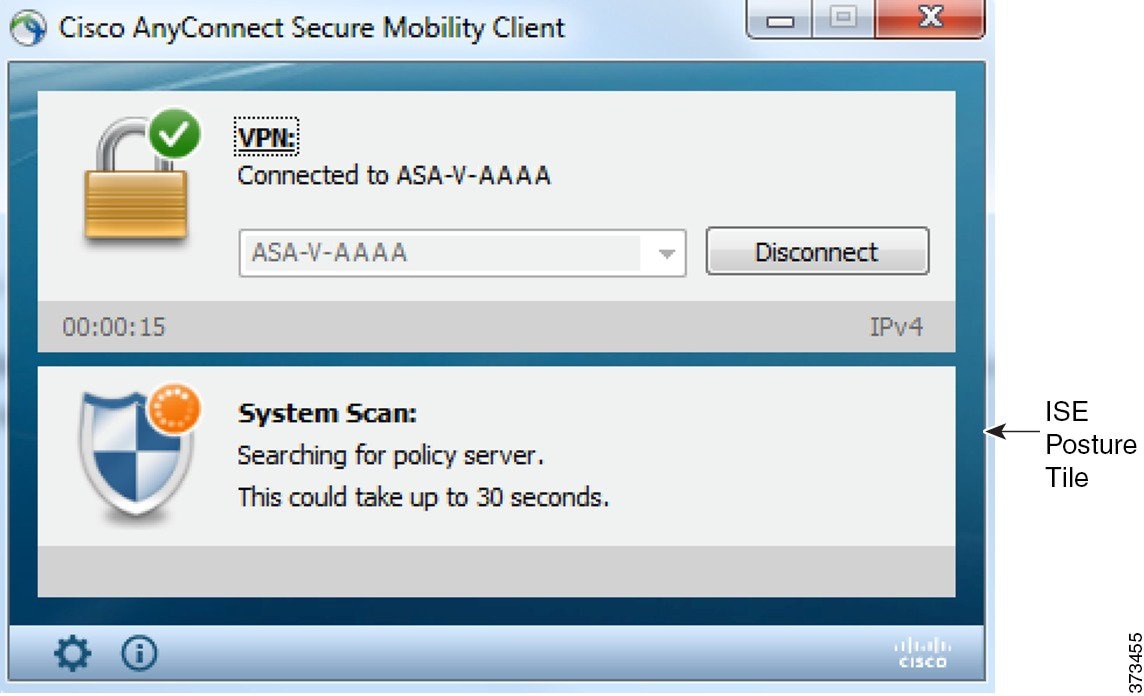
Status of ISE Posture
When AnyConnect ISE Posture is working and blocking network access as expected, you see "System Scan: Searching for policy server" in the ISE Posture tile of the AnyConnect UI. In the Windows Task Manager or macOS system log, you can see that the process is running. If the service is not running, you see "System Scan: Service is unavailable" in the ISE Posture tile of the AnyConnect UI.
A network change starts the discovery phase. With AnyConnect ISE Posture, if the default route of the primary interface is changed, it brings the agent back to the discovery process. For example, when WiFi and the primary LAN are connected, the agent restarts discovery. Likewise, if WiFi and the primary LAN are connected but then WiFi becomes disconnected, the agent will not restart discovery.
You may also see the following status messages after "System Scan" in the ISE Posture tile of the AnyConnect UI:
- Limited or no connectivity—No discovery is occurring because you have no connection. The AnyConnect ISE Posture agent may be performing discovery on the wrong endpoint on the network.
-
System scan not required on current WiFi—No discovery is occurring because an unsecured WiFi was detected. The AnyConnect ISE Posture agent only starts discovery on the LAN, on the wireless if 802.1X authentication is used, and on the VPN. The WiFi may be unsecured, or you disabled the feature by setting OperateOnNonDot1XWireless to 1 in the agent profile.
-
Unauthorized policy server—The host does not match the server name rule of the ISE network so there is limited or no network access.
-
The AnyConnect Downloader is performing update...—The downloader is invoked and compares the package versions, downloads the AnyConnect configuration, and performs the necessary upgrades.
-
Scanning System...—Scanning for antivirus and antispyware security products has started. If the network is changed during this process, the agent recycles the process of generating the log file, and the status goes back to "No policy server detected."
-
Bypassing AnyConnect scan—Your network is configured to use the Cisco NAC agent.
-
Untrusted Policy Server Cancelled by the user—When you unblock the connection to untrusted servers in the AnyConnect UI with the System Scan Preferences tab, you receive the AnyConnect Downloader's Security Warning in a popup window. When you click Cancel Connection on this warning page, the ISE Posture tile changes to this status.
-
Network Acceptable Use Policy—The access to the network requires that you view and accept the Acceptable Use Policy. Declining the policy may result in limited network access.
-
Updating Network Settings—In the ISE UI in Settings > Posture > General Settings, you can specify how many seconds of delay should occur between network transitions.
-
Not Compliant. Update time expired.—The time set for remediation has expired.
-
Compliant. Network access allowed.—The remediation is complete. The System Scan > Scan Summary also shows the status as complete.
-
No policy server detected—The ISE network is not found. After 30 seconds, the agent slows down probing. The default network access takes effect.
Posture and Multi Homing
AnyConnect ISE posture module does not support multi homing because its behavior for such scenarios is undefined. For example, when media changes from wired to wireless and them back to wired, the user may see a posture status status of compliant from the ISE posture module even though the endpoint is actually in redirect on the wired connection.
Simultaneous Users on an Endpoint
AnyConnect ISE does not support separate posture assessment when multiple users are logged onto an endpoint simultaneously sharing a network connection. When the first user to run AnyConnect ISE is successfully postured, and the endpoint is granted trusted network access, all other users on the endpoint inherit the network access. To prevent this, the administrator can disable features that allow simultaneous users on the endpoint.
Logging for Posture Modules
For ISE Posture, events are written to the native operating system event logs (Windows Event Log Viewer or macOS system log).
For VPN Posture (HostScan), any errors and warnings go to syslogs (for non-Windows) and to the event viewer (for Windows). All available messages go to the log files.
The VPN Posture (HostScan) module components output up to three logs based on your operating system, privilege level, and launching mechanism (Web Launch or AnyConnect):
-
cstub.log—Captures logging when AnyConnect web launch is used.
-
libcsd.log—Created by the AnyConnect thread that uses the VPN Posture API. Debugging entries are made in this log depending on the logging level configuration.
-
cscan.log—Created by the scanning executable (cscan.exe) and is the main log for VPN posture. Debugging entries are made in this log depending on the logging level configuration.
Posture Modules' Log Files and Locations
For ISE Posture, events are contained in their own subfolder of the installed AnyConnect version, making them easy to isolate from the rest of the AnyConnect events. Each viewer allows the searching of keywords and filtering. The Web Agent events write to the standard application log.
For troubleshooting purposes, the ISE Posture requirement policy and assessment reports are logged, but to a separate, obfuscated file on the endpoint rather than to the event logs. Some log file sizes, such as aciseposture, can be configured by the administrator in the profile; however, the UI log size is predefined.
Whenever a process terminates abnormally, a mini dump file is generated, just as other AnyConnect modules provide.
For VPN Posture (HostScan), the files are located in the users home folder in the following directory:
-
(Non-Windows)—.cisco/hostscan/log
-
(Windows)— C:\Users\<user_name>\AppData\Local\Cisco HostScan\log\cscan.log
ISE Posture Profile Editor
An administrator can choose to use the standalone editor to create the posture profile and then upload it to ISE. Otherwise, the embedded posture profile editor is configured in the ISE UI under Policy Elements. When the AnyConnect configuration editor is launched in ISE, it creates the AnyConnect configuration complete with AnyConnect software and its associated modules, profiles, OPSWAT, and any customization. The standalone profile editor for ISE Posture in ASA contains the following parameters:
-
Agent Behavior
-
IP Address Change
For the optimal user experience, set the values below to our recommendations.
-
VLAN detection interval—Interval at which the agent tries to detect VLAN changes before refreshing the client IP address. The valid range is 0 to 900 seconds, and the recommended value is 5 seconds.
-
Ping or ARP—The method for detecting IP address changes. The recommended setting is ARP because the default gateway might be configured to block ICMP packets.
-
Maximum timeout for ping—The ping timeout from 1 to 10 seconds.
-
Enable agent IP refresh—Check to enable VLAN change detection.
-
DHCP renew delay—The number of seconds the agent waits after an IP refresh. Configure this value when you have Enable Agent IP Refresh enabled. If this value is not 0, the agent will do an IP refresh during this expected transition. If a VPN is detected during the refresh, the refresh will be disabled. The valid values are 0 to 60 seconds, and the recommended value is 5 seconds.
-
DHCP release delay— The number of seconds the agent delays doing an IP refresh. Configure this value when you have Enable Agent IP Refresh enabled. If this value is not 0, the agent will do an IP refresh during this expected transition. If a VPN is detected during the refresh, the refresh will be disabled. The valid values are 0 to 60 seconds, and the recommended value is 5 seconds.
-
Network transition delay—The timeframe (in seconds) for which the agent suspends network monitoring so that it can wait for a planned IP change. The recommended value is 5 seconds.
-
-
Posture Protocol
-
Discovery host—The server to which the agent can connect. For standalone profile editors, enter a single host only.
-
Server name rules—A list of wild-carded, comma-separated names that defines the servers to which the agent can connect (such as .cisco.com).
-
PRA retransmission time—When a passive reassessment communication failure occurs, this agent retry period is specified. The valid range is 60 to 3600 seconds.
-
Advanced Panel
The Advanced Panel of the AnyConnect Secure Mobility Client UI is an area for each component to display statistics, user preferences, and any extra information specific to the component. If you click the Advanced Window for all components icon on the AnyConnect system tray, the new System Scan section contains the following tabs:
 Note | These statistics, user preferences, message history, and such are displayed under the Statistics window on macOS. Preferences are in the Preferences window and not in a tab orientation as in Windows. |
- Preferences—Allows you to block connections to untrusted servers so that during the downloader process, you receive an "Untrusted Server Blocked" message for any ISE server that has untrusted certification and is unverified. If you disable the blocking, AnyConnect will not block connections to potentially malicious network devices.
- Statistics—Provides current ISE Posture status (compliant or not), OPSWAT version information, the status of the Acceptable Use Policy, the last running time stamp for posture, any missing requirements, and any other statistics deemed important enough to display for troubleshooting purposes.
- Security Products—Accesses the list of antivirus and antispyware products installed on your system.
- Scan Summary—Allows the users to see whatever posture items the administrator configured for them to see. For example, when configured, they could see all of the items that have been postured on their system or only the ones that failed the posture check and required remediation.
- Message History—Provides a history of every status message sent to the system tray for a component. This history is useful for troubleshooting.
What VPN Posture (HostScan) Module Provides
HostScan
HostScan is a package that installs on the remote device after the user connects to the ASA and before the user logs in. HostScan consists of any combination of the basic module, the endpoint assessment module, and the advanced endpoint assessment module. HostScan is not supported with mobile devices (Android, iOS, Chrome, or UWP).
 Note | In AnyConnect release 3.x, this package was bundled in the hostscan_version.pkg file, which must be updated in ASA under HostScan image and enabled to get HostScan functioning. It is now a separate install. |
Basic Functionality
HostScan automatically identifies operating systems and service packs on any remote device establishing a Cisco clientless SSL VPN or AnyConnect VPN client session.
You can also configure HostScan to inspect the endpoint for specific processes, files, and registry keys. It performs all of these inspections before full tunnel establishment and sends this information to the ASA to distinguish between corporate-owned, personal, and public computers. The information can also be used in assessments.
 Note | Pre-login assessment and returning certificate information is not available. HostScan is not an authentication method; it simply checks to verify what exists on the device attempting to connect. |
HostScan also automatically returns the following additional values for evaluation against configured DAP endpoint criteria:
-
Microsoft Windows, macOS, and Linux operating systems
-
Microsoft Knowledge Base numbers (Kbs)
-
Device endpoint attributes types such as host name, MAC address, BIOS serial number, port numbers (legacy attribute), TCP/UDP port number, privacy protection, and version of endpoint assessment (OPSWAT)
 Note | HostScan gathers service release (GDR) information about Microsoft software updates on a Windows client system. A service release contains multiple hotfixes. The service release endpoint attribute is used in DAP rules, not hotfixes. |
Endpoint Assessment
Endpoint Assessment is a HostScan extension that examines the remote computer for a large collection of antivirus and antispyware applications, associated definitions updates, and firewalls. You can use this feature to combine endpoint criteria to satisfy your requirements before the ASA assigns a specific dynamic access policy (DAP) to the session.
See the Dynamic Access Policies section in the appropriate version of the Cisco ASA Series VPN Configuration Guide for details.
Advanced Endpoint Assessment:Antivirus, Antispyware, and Firewall Remediation
On Windows, Mac OS X, and Linux desktops, Advanced Endpoint Assessment can attempt to begin remediation of various aspects of antivirus, antispyware, and personal firewall protection if that software allows a separate application to begin remediation.
Antivirus—Remediate these components of antivirus software:
-
Force File System Protection—Enable antivirus software that is disabled.
-
Force Virus Definitions Update—Begin an update of virus definitions, if the antivirus definitions have not been updated in the number of days defined by the Advanced Endpoint Assessment configuration.
Antispyware—Begin an update of antispyware definitions, if the antispyware definitions have not been updated in the number of days defined by the Advanced Endpoint Assessment configuration.
Personal Firewall—Reconfigure firewall settings and rules that do not meet the requirements defined in the Advanced Endpoint Assessment configuration. For example,
-
Enable or disable the firewall.
-
Prevent or allow applications to run.
-
Block or open ports.

Note
Not all personal firewalls support this feature.
If the end user disables antivirus or personal firewall after successfully establishing the VPN connection, our Advanced Endpoint Assessment feature attempts to re-enable that application within approximately 60 seconds.
Configure Antivirus Applications for HostScan
Before installing the VPN Posture (HostScan) module, configure your antivirus software to "white-list" or make security exceptions for these applications below. Antivirus applications can misinterpret the behavior of these applications as malicious:
-
cscan.exe
-
ciscod.exe
-
cstub.exe
Integration with Dynamic Access Policies
The ASA integrates the HostScan features into dynamic access policies (DAPs). Depending on the configuration, the ASA uses one or more endpoint attribute values in combination with optional AAA attribute values as conditions for assigning a DAP. The HostScan features supported by the endpoint attributes of DAPs include OS detection, policies, basic results, and endpoint assessment.
You can specify a single attribute or combine attributes that form the conditions required to assign a DAP to a session. The DAP provides network access at the level that is appropriate for the endpoint AAA attribute value. The ASA applies a DAP when all of its configured endpoint criteria are satisfied.
See the Configure Dynamic Access Policies section in the Cisco ASA Series VPN Configuration Guide.
BIOS Serial Number in a DAP
VPN Posture (HostScan) can retrieve the BIOS serial number of a host. You can use a Dynamic Access Policy (DAP) to allow or prevent a VPN connection to the ASA based on that BIOS serial number.
Specify the BIOS as a DAP Endpoint Attribute
Procedure
| Step 1 | Log on to ASDM. |
| Step 2 | Choose or . |
| Step 3 | In the Configure Dynamic Access Policies panel, click Add or Edit to configure BIOS as a DAP Endpoint Attribute. |
| Step 4 | To the right of the Endpoint ID table, click Add. |
| Step 5 | In the Endpoint Attribute Type field, select Device. |
| Step 6 | Check the BIOS Serial Number checkbox, select = (equals) or != (not equals), and enter the BIOS number in the BIOS Serial Number field. Click OK to save changes in the Endpoint Attribute dialog box. |
| Step 7 | Click OK to save your changes to the Edit Dynamic Access Policy. |
| Step 8 | Click Apply to save your changes to the Dynamic Access Policy. |
| Step 9 | Click Save. |
How to Obtain BIOS Serial Numbers
-
Windows—http://support.microsoft.com/kb/558124
-
macOS—http://support.apple.com/kb/ht1529
-
Linux—Use this command:
/usr/bin/hal-get-property --udi /org/freedesktop/Hal/devices/computer --key system.hardware.serial
Determine the HostScan Image Enabled on the ASA
Open ASDM and choose Configuration > Remote Access VPN > HostScan Image.
Upgrade HostScan
If you are upgrading AnyConnect and HostScan manually (using msiexec), make sure that you first upgrade AnyConnect and then HostScan.
OPSWAT Support
AnyConnect's VPN (Hostscan) Posture and ISE Posture modules both use the OPSWAT framework to secure endpoints.
This framework, that involves both the client and the headend, assists in the assessment of third-party applications on the endpoint. The version of OPSWAT used in the client and the headend must match. Support charts are provided for each posture method that contain product and version information for the list of applications recognized by the OPSWAT versions used.
When there is a mismatch in the version number between the headend (ASA or ISE) and the endpoint (VPN posture or ISE posture), the OPSWAT compliance module gets upgraded or downgraded to match the version on the headend. These upgrades/downgrades are mandatory and happen automatically without end user intervention, as soon as a connection to the headend is established.
VPN Hostscan Posture OPSWAT Support
The HostScan Support Charts correspond to the HostScan package version which provides HostScan posture in AnyConnect working with an ASA headend.
HostScan is versioned to coordinate with AnyConnect major and maintenance releases. You specify the HostScan version when you configure the HostScan package in ASDM at Configuration > Remote Access VPN > Secure Desktop Manager > Host Scan Image.
VPN HostScan Posture guidelines:
-
All versions of HostScan use OPSWAT v2. OPSWAT v3 is not supported in any version of HostScan.
ISE Posture OPSWAT Support
Cisco AnyConnect Agent Compliance Modules are for the ISE Posture Module.
ISE Agent Compliance Modules version reflects the base OPSWAT version. In ISE posture, the OPSWAT binaries are packaged into a separate installer. You can manually load the OPSWAT library to the ISE headend from the local file system, or configure ISE to obtain it directly using the ISE Update Feed URL.
Only the OPSWAT v3 library can be uploaded to ISE.
Bios Agent Plus Full Espaã±ol Crack Serial
Source: https://www.cisco.com/c/en/us/td/docs/security/vpn_client/anyconnect/anyconnect40/administration/guide/b_AnyConnect_Administrator_Guide_4-0/configure-posture.html
Belum ada Komentar untuk "Bios Agent Plus Full Espaã±ol Crack Serial"
Posting Komentar